Hostwinds Tutorials
Search results for:
Table of Contents
SSH Key vs Password Based Authentication
Tags: Security
What Are the Benefits of SSH Key-Based Authentication?
SSH (Secure Shell) is an open-source -- and most trusted -- network protocol for logging into servers remotely. This allows the execution of commands and programs through the server itself. SSH may also transfer files between computers over the network using Secure Copy (SCP) protocol. The best way to ensure the server's security is to use SSH Keys.
SSH Keys are a way to secure your server further against malicious activities directed at trying to SSH into your server. SSH Keys provide authorization that can only be fulfilled by those who have ownership of the private key associated with the public key on the server. An unwanted visitor may be able to get access to the server's public key. Still, without the associated private key, they will be unable to access the server, even if they know the password.
With an SSH Key set up, you can also safely log in to your server without needing a password. The server will require the connecting computer to have the private key associated with the server's public key to connect. As a result, with or without the password, only users with the private key generated with the public key can gain access.
How Do I Setup Key-Based Authentication?
The following guide will help you create a public / private key pair, get them installed and ready to use for your SSH server;
Local Linux/Mac OS to Remote Linux Server (Cloud/Dedicated)
Step 1: Enter the following command locally
$ ssh-keygen -t rsa
This will generate two files in your hidden ~/.ssh directory
- id_rsa – your private key
- id_rsa.pub – your public key
Step 2: Choose whether or not you want a password upon setup; Hit "Enter" to set no password. Otherwise, type the password to be used and then hit "Enter" afterward.
NOTE: When you add a passphrase to the SSH key, it will require both the private key and the passphrase when logging into the server.
Step 3: Set the Permissions on your folders and private key. This makes them only accessible as the owner of the files.
chmod 700 ~/.ssh
chmod 600 ~/.ssh/id_rsa
Step 4: Copy and install your public key (id_rsa.pub) to the server's authorized_keys list.
cat ~/.ssh/id_rsa.pub > ~/.ssh/authorized_keys
Note: Ensure backup and authorized keys before making changes to this file, or they will be lost.
Step 5: Set your server permissions. This makes the folder only accessible to the owner of the folder.
chmod 600 ~/.ssh/authorized_keys
Step 6: Set Proper SELinux context
restorecon -Rv ~/.ssh
How to use an SSH Key?
To use the SSH key, you will need to use the private key and public key. Start by saving each to a local file on your computer. However, each SSH Client will be different on how to enter the private and public keys. Some may require you to upload the files you created with the SSH key information, while others may ask you to copy and paste the information into the SSH Client.
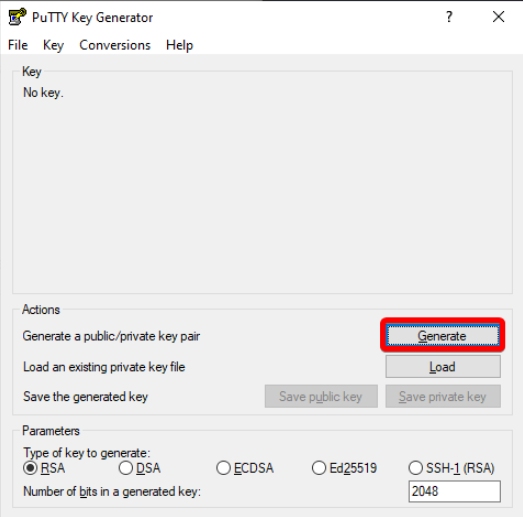
If you have an SSH client installed, such as PuTTY, it should also come with a program called PuTTYgen. PuTTYgen will help you create an SSH key based on your random inputs.
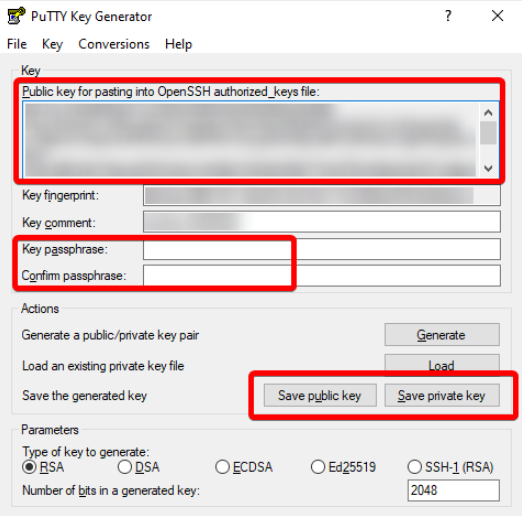
It will also help you to make the keys in the format PuTTY requires. Click the Save Public/Private Key. You can also copy your Public Key from the box at the top, indicated by the arrow. The public key is what you will need to enter on your server to permit people logging in with the private key access to the server. You can also generate a Key Phrase from PuTTYgen as well.
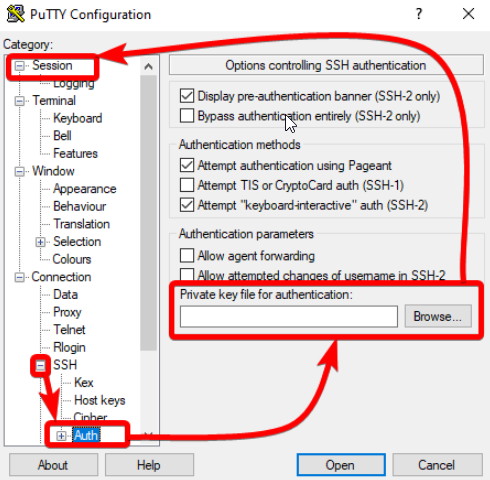
To add the private key to PuTTY, Click on the + by the SSH option in the window, then click Auth. On this page, browse to your Private key. Then Click back on Session to log in. You can save this configuration on the lower half of the session window.
SSH Key through PuTTY
If you wish to know how to set up an SSH key for your Cloud VPS service, we have provided a step-by-step instructional guide for your convenience. Setting up the SSH Key through PuTTY, you will need to upload the public key to the server (Commonly done through FTP or SFTP)
Written by Hostwinds Team / June 5, 2021
